Online IP lookup: Can it detect proxy IPs? Instantly spot your real IP vs. anonymous proxies.
Recently, many friends have been asking: can online IP lookup really accurately identify proxy IPs? Can it instantly distinguish between a real IP and an anonymous proxy?
In fact, a simple online IP lookup usually only reveals surface-level information. To truly identify proxies, you need deeper proxy detection logic combined with multi-dimensional analysis tools.
Today, let’s walk through this with some practical experience and talk about whether online IP lookup can detect proxy IPs—and whether it can really distinguish between real IPs and anonymous proxies.

1. Online IP Lookup — What Can It Actually Show?
Many people assume that entering an IP address into a lookup tool will reveal “who this person is.” In reality, that’s not how it works.
Typical IP lookup tools can show:
• IP geolocation (country, province/state, city)
• ISP information (telecom carriers, cloud providers, data centers)
• Network type (residential broadband / data center)
• Approximate geographic location
• Whether it is a known proxy or tool node (supported by some tools)
In other words, online IP lookup is more about “network profiling” than “identity identification.”
2. Can Proxy Detection Really Be 100% Accurate?
The key concern is reliability—can proxy detection truly identify real IPs? Common methods include:
1. IP Database Matching
The system compares the IP against known VPNs, proxy pools, and data center IP databases. If matched, it gets labeled as a proxy.
2. Behavioral Analysis
For example: frequent IP switching in a short time, access from multiple regions, abnormal request patterns (crawler behavior).
3. Network Type Identification
If the IP belongs to a data center (IDC), it is often flagged as high risk—even if it’s not technically a VPN.
So proxy detection is more about “risk assessment” rather than absolute identification.
3. Why Is It Hard to Distinguish Real IPs from Anonymous Proxies?
Many assume IP lookup tools can directly reveal the “real IP,” but the situation is more complex.
1. NAT and Shared IPs Are Common
Many home and corporate networks share a single public IP, which complicates identification.
2. Advanced Anonymous Proxy Technology
Modern proxies—especially residential proxies—simulate normal user environments, making them hard to detect at the IP level.
3. Proxy Behavior Mimics Real Users
Some anonymous proxy services intentionally imitate normal browser behavior, making detection even harder.
4. Browser Fingerprinting Is More Important Than IP
If IP is like a “street address,” browser fingerprinting is like a “behavioral identity.”
• Modern risk control systems analyze browser version, OS, WebGL, Canvas, timezone, and language.
• Even if the IP changes, the system can still identify anomalies through fingerprinting.
Therefore, browser fingerprinting is often more important than IP detection in modern security systems.
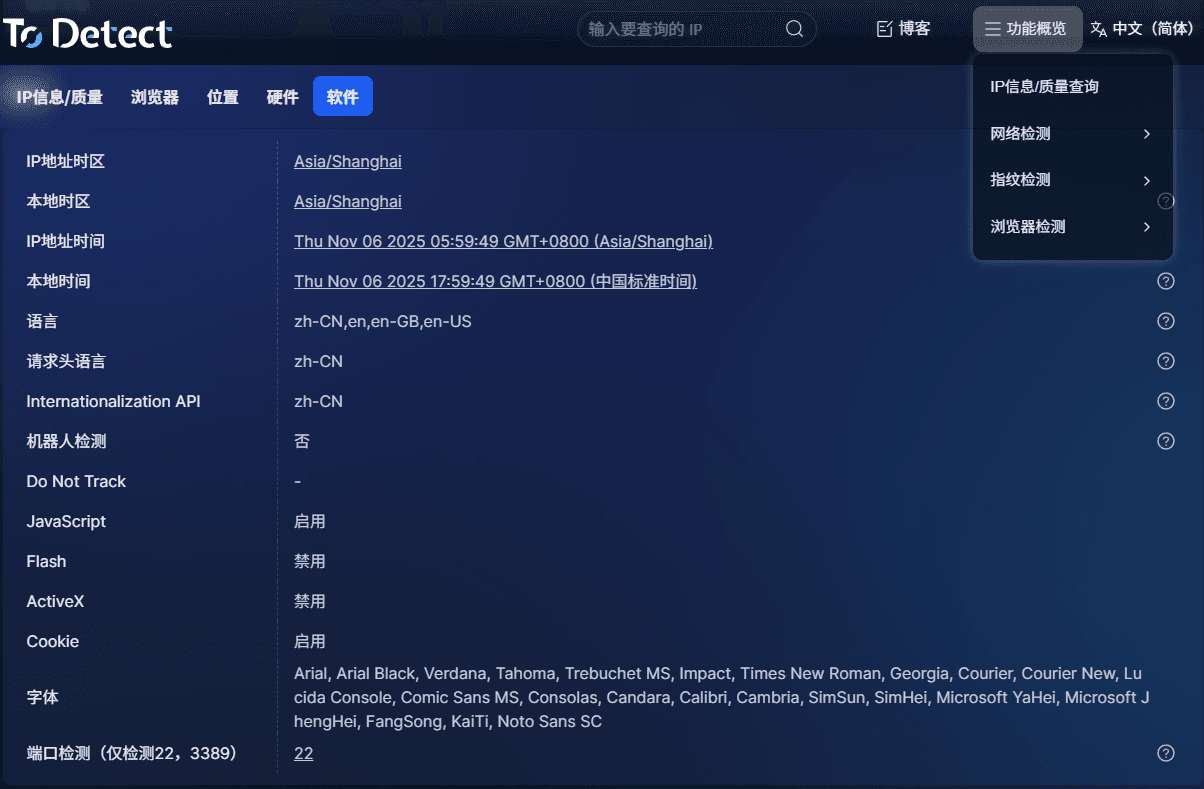
5. ToDetect: A Unified Detection Approach
Among various tools, the ToDetect platform not only provides IP lookup but also integrates multi-dimensional analysis:
• Combines geolocation, proxy detection models, browser fingerprinting, and risk scoring
• Not only tells you “where the IP is” but also whether the behavior looks like a real user
• More valuable for anti-fraud, ad verification, and account security
6. IP Lookup Tools — How to Choose a Reliable One?
1. Check the Data Sources
Does the tool continuously update global IP databases? Does it include ASN, ISP, and blacklist data?
Professional tools break IP data into:
• Country / city location
• ISP / cloud provider / data center
• ASN (Autonomous System Number)
• Data center IP identification
• Suspected proxy/VPN detection
If a tool only shows “city + country,” it’s basic at best.
2. Must Support Proxy Detection
Today, the main goal of IP lookup is often proxy detection—not just geolocation.
A good tool should include proxy recognition, data center detection, risk scoring, and blacklist matching.
3. Browser Fingerprinting Is a Big Plus
Advanced tools combine IP data with fingerprinting:
Canvas, WebGL, fonts, timezone, language, WebRTC leaks, etc.
4. Cross-Verification Matters
Reliable tools compare multiple data sources to avoid false positives.
Consistency across databases, location conflicts, ASN anomalies, and proxy signals all matter.
5. Speed and API Capability
For enterprise use (fraud detection, ads, bulk analysis), you need:
• Fast response time (within seconds)
• API support for batch queries
• Log export
• Automation support
7. Online IP Lookup — FAQ (IP & Proxy Detection)
1. Can IP lookup identify a specific person?
No. It can only show approximate location, ISP, and network type.
2. Why is the IP location sometimes inaccurate?
Due to dynamic IP allocation, mobile networks, routing, and database delays.
3. Can proxy detection be 100% accurate?
No. Especially with residential or high-anonymity proxies—it’s usually risk-based, not absolute.
4. IP vs Browser Fingerprinting?
IP shows “where you are,” fingerprinting shows “who you behave like.”
Bottom Line
Online IP lookup provides basic network information and helps identify proxies to some extent—but it’s only one layer of a broader risk control system.
True accuracy comes from multi-dimensional analysis. Tools like ToDetect integrate these signals to turn IP lookup from simple “location checking” into “risk evaluation.”




