Same accounts on phone and PC: Linked? How device fingerprinting works
Recently, many friends involved in cross-border multi-account operations have been asking me: if you log into multiple accounts simultaneously on both a phone and a computer, will the platform still detect them as linked accounts?
In reality, modern platform risk-control systems are far more complex than most people imagine. They don't just check your network environment — they also analyze device fingerprints, browser fingerprints, and many other dimensions.
Today, let's talk about how platforms actually connect multiple accounts through device information, and also share some practical anti-linking strategies for multi-account management.

1. If You Log Into Multiple Accounts on Both Phone and Computer, Will They Be Linked?
Many people assume that using separate phones and computers for different accounts is enough to stay safe. In reality, modern platform risk-control systems are not as simple as checking whether accounts are logged in from the same device.
Platforms no longer rely on a single condition — they build a comprehensive behavioral profile, including:
• Whether the IP address is the same
• Whether the device environment is similar
• Whether browser information overlaps
• Whether login behavior appears abnormal
• Whether Cookie / local storage data is shared
In other words, even if you use both a phone and a computer to log into multiple accounts, they may still be detected as linked accounts if the environment characteristics are highly similar.
2. What Is Device Fingerprinting and Why Is It So Important?
Device Fingerprinting means platforms identify users not through their accounts, but through unique device characteristics.
Even if you clear cache or switch accounts, the system can still recognize you as the same operator if the device fingerprint remains unchanged.
Common device fingerprint information includes:
• Operating system version (Windows / iOS / Android)
• Screen resolution
• Time zone and language settings
• GPU / Canvas rendering characteristics
When combined, these details create a highly unique signature, which is why modern risk-control systems rely heavily on device fingerprinting to identify account relationships.
3. Browser Fingerprinting: More Detailed Than You Think
Platforms also identify users through browser environments, including User-Agent information, Cookies, LocalStorage, Canvas rendering fingerprints, and more.
Many people believe changing IP addresses is enough, but if the browser fingerprint remains the same, platforms may still identify the accounts as operated by the same person.
These risks are especially common in:
• Cross-border e-commerce multi-store operations
• Social media account matrix management
• Bulk advertising account management
• Overseas account warming activities
This is why isolated browser environments have gradually become essential.
4. Common Multi-Account Environment Risk Reference Table
| Usage Scenario | Risk Level | Possible Trigger | Suggested Optimization |
|---|---|---|---|
| Logging into multiple accounts in the same browser | High Risk | Repeated browser fingerprint detection | Use isolated browser environments or separate configurations |
| Logging into the same batch of accounts on both phone and computer | Medium-High Risk | Highly similar device fingerprints | Separate devices and environments for account management |
| Frequently switching accounts under the same IP | High Risk | Strong IP association | Use different IP ranges or dynamic IP strategies |
| Highly synchronized multi-account behavior | Medium Risk | Abnormally similar behavior models | Distribute operation times and behavior patterns |
| Using identical browser extension combinations | Medium Risk | Matching extension fingerprints | Reduce extension duplication |
| Bulk account registration without environment testing | Extremely High Risk | No isolation + repeated fingerprints | Test the device environment before registration (e.g. ToDetect) |
| Using fixed devices for long-term account warming | Medium Risk | Stable long-term fingerprints are easy to classify | Moderately vary environment parameters to reduce consistency |
5. How Platforms Actually “Link” Multiple Accounts
The logic is actually quite simple: multi-dimensional cross-analysis. This usually includes:
🔶 IP address association — multiple accounts logged in from the same IP or frequent IP changes with identical behavior patterns
🔶 Device fingerprint consistency — repeated use of the same device environment
🔶 Browser fingerprint overlap — identical Canvas / WebGL / font characteristics
🔶 Behavioral model analysis — highly similar login times and operation rhythms
🔶 Account interaction relationships — mutual follows, interactions, and batch actions
So-called “multi-account anti-linking” is essentially about reducing overlap across these dimensions.
6. Practical Multi-Account Anti-Linking Strategies
1. Account Layering: Assign Different Roles First
Many people immediately start creating multiple accounts, but the first step should actually be account categorization:
• Main accounts (core operations / payment / brand accounts)
• Support accounts (warming accounts, content preparation, interaction accounts)
• Test accounts (creative testing, strategy testing)
Different account levels should use completely isolated environments and should never share the same browser configuration or device environment long-term.
2. IP Management: It's More Than Just “Changing IPs”
Many people think anti-linking simply means “one IP per account,” but in reality, strategies should be more refined:
• Fixed residential IPs (stable accounts): for long-term operational accounts requiring stable environments
• Dynamic IPs (support accounts): for testing and lightweight operations
• Strict IP range isolation (sensitive accounts): avoid exposing different business lines under the same IP segment
⚠️ Important: frequent IP changes combined with identical login behavior can also trigger platform risk controls.
3. Browser Environment Isolation: The Core Priority
Platforms identify not only IP addresses, but also the entire browser environment, including Canvas fingerprints, WebGL rendering, User-Agent information, and more.
It is recommended that each account use an independent browser environment. Avoid switching between multiple accounts under the same Chrome profile and avoid sharing browser extensions.
4. Cookie and Local Storage Isolation
Many platforms determine whether users share the same usage trajectory through:
• Cookies
• LocalStorage
• SessionStorage
These data points help identify whether multiple accounts belong to the same operator.
Avoid sharing browser environments across accounts. Regularly clear or isolate storage data, and avoid repeatedly logging into different accounts within the same browser container.
5. Use Environment Detection Tools in Advance (e.g. ToDetect)
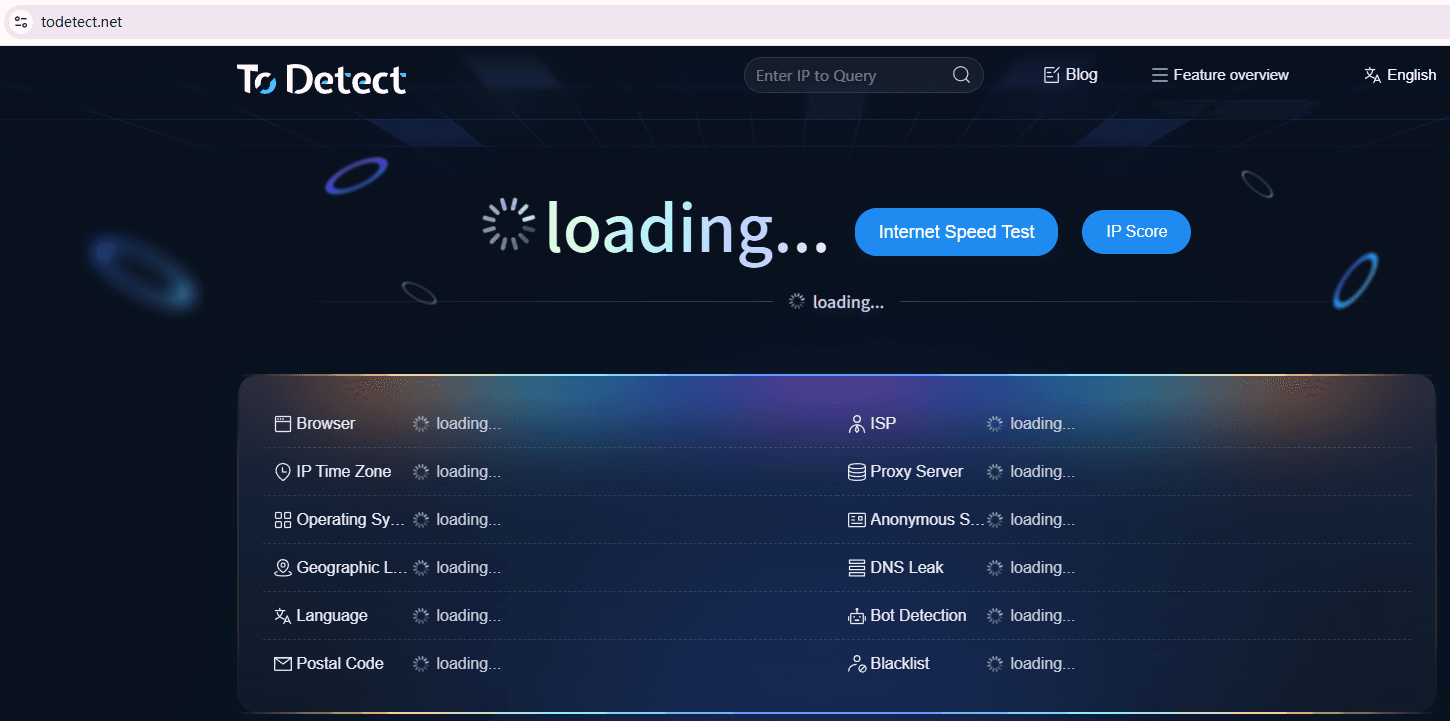
Isolation alone does not guarantee safety — you also need to verify whether the isolation is actually effective. Tools like ToDetect are valuable because they can:
• Check whether the current browser fingerprint is unique
• Determine whether multiple environments share duplicate characteristics
• Detect hidden linking risks in advance
• Verify whether IP and device matching appears reasonable
These tools cannot “prevent bans,” but they can help determine whether your multi-account environment setup is truly isolated correctly.
6. Final Key Principle: Avoid a Fully Automated Mindset
Many people managing multiple accounts tend to go to extremes — either completely manual operations or fully automated scripting.
In reality, a more stable approach is semi-automation combined with human behavior rhythms and environment isolation.
Especially as platform risk-control systems become more intelligent, fully machine-driven behavior becomes easier to detect.
7. The Misconception About “Complete Anti-Linking”
It must be emphasized that no method can guarantee complete anti-linking.
• Claims such as “absolutely no bans” or “completely isolated environments” are unrealistic in practice.
• Platform risk-control systems are constantly evolving and evaluate overall risk probability rather than relying on a single factor.
Therefore, the more realistic strategy is reducing linkage probability rather than pursuing absolute isolation.
Conclusion:
Whether you use phones or computers, highly overlapping device characteristics and browser environments can still trigger platform risk controls and lead to account linkage detection.
Whether you're working in e-commerce, social media, or advertising, the key is not simply “running multiple accounts,” but designing properly isolated multi-account environments.
Multi-account security is not about “hiding deeply” — it’s about whether your environment behaves like a real human user. If you're managing an account matrix, this is especially important.