Fingerprint browsers for cross-border: still profitable? A beginner's zero‑to‑one guide
Recently, many people have been asking whether it's still worth using fingerprint browsers for cross-border business projects, and whether beginners still have a chance to make money with them.
In the past, you could casually register a few accounts and start running ads, operating stores, or posting content. But things are different now — platform risk control systems are becoming much stricter.
Next, this article will clearly explain the real-world use cases of fingerprint browsers in cross-border projects, environment setup strategies, and how beginners can go from 0 to 1 step by step while avoiding unnecessary mistakes.

1. What Is a Fingerprint Browser and Why Is It Essential in Cross-Border Business?
A fingerprint browser is essentially a tool that simulates independent computer environments.
Platforms such as e-commerce sites, advertising systems, and social media platforms use browser fingerprint detection to determine whether multiple accounts are operated by the same person and whether those accounts are connected.
That’s why multi-account operations in cross-border businesses almost always rely on fingerprint browsers.
2. Why Are Fingerprint Browsers Necessary for Cross-Border Projects?
If you’ve worked in cross-border e-commerce or social media matrix operations, you already know the biggest pain point: account linking and bans.
• Especially for Facebook multi-account advertising, TikTok matrix operations, Amazon/independent store support accounts, and Shopee/Lazada multi-store management.
• Once the platform detects identical browser fingerprints, it may restrict logins, trigger risk controls, or directly ban accounts.
• The purpose of a fingerprint browser is to make every account appear as if it is running on a completely separate computer.
3. Fingerprint Browser Environment Configuration Checklist (Practical Reference)
| Project Aspect | Recommended Setup / Practice | Common Mistakes | Practical Advice |
|---|---|---|---|
| Fingerprint Browser Selection | Choose tools with stable updates and environment isolation support (such as BitBrowser-like tools) | Only caring about free or cheap options while ignoring stability | Prioritize products with long-term maintenance and updates |
| Browser Fingerprint Environment | Each account should have unique Canvas/WebGL/fonts/resolution settings | Using the same template environment for multiple accounts | One account = one environment is the minimum standard |
| IP Configuration | Prefer residential IPs and match the account’s target region | Using free proxies or datacenter IPs | IP quality matters more than quantity |
| Cookie Management | Store cookies separately for each account | Sharing cookies between multiple accounts | Clean regularly but never mix them |
| Browser Fingerprint Detection | Use detection tools like ToDetect before going live | Operating without testing | Risk-control testing before launch is mandatory |
| Account Operation Rhythm | Warm up accounts first, then gradually scale up | Performing large-scale operations immediately on new accounts | The first 7 days determine account survival |
4. Checking Whether the Fingerprint Browser Environment Is Clean
Before logging into accounts officially, many people overlook a critical step: checking whether the environment is clean.
• Browser fingerprint detection tools can help determine whether real device information is exposed, whether the fingerprint is unique, and whether high-risk features exist.
• ToDetect mainly helps analyze browser fingerprint exposure levels, simulate platform risk-control checks, and determine whether the environment appears “human-like.”
👉 In simple terms: launching without testing is like operating while sick.
5. Beginner’s Guide: From 0 to 1 with Fingerprint Browsers (Core Practical Tips)
Step 1: Understand That “Environment = Account Container”
In BitBrowser, the most important concept is that one browser environment equals one independent “virtual computer” for an account.
• Each environment = a brand-new computer
• Each environment = fully isolated data
• Each environment = no shared cookies or cache
So when cross-border operators talk about “multi-opening,” they’re not referring to opening multiple browsers — they mean running multiple isolated environments.
Step 2: Create Your First Fingerprint Browser Environment
After entering BitBrowser, you’ll see the “Create Environment” option. Beginners can configure it like this:
🔶 Basic Naming
Examples: FB Account 01, TikTok US01, Store A. Use organized names for easier management later.
🔶 Fingerprint Parameter Settings (Important)
In the fingerprint configuration section, avoid randomly changing advanced parameters. Reasonable randomization is enough:
• Operating System: Random Windows / Mac
• Browser Kernel: Default or recommended version
• Resolution: Randomized (avoid identical settings)
• Language: Match the IP region
• Time Zone: Automatically match the IP region
⚠️ Key Principle: Don’t make all environments look identical. This step builds your browser fingerprint isolation layer.
Step 3: Bind an IP Address (The Key to Success or Failure)
• Many beginners get banned not because of the browser itself, but because of IP problems. BitBrowser allows direct proxy IP binding.
• Residential IPs are recommended first, while static IPs are better for long-term accounts. The country/region should match the target market.
⚠️ Avoid free proxies, constantly switching IPs, or using one IP for many accounts.
Step 4: First Login (Critical “Environment Warming” Period)
During the first login, don’t rush into operations. Recommended process:
• Day 1: Only log in, browse the homepage, no likes or comments
• Days 2–3: Browse content normally and simulate real user behavior
• Days 4–5: Start light interactions (likes/favorites). This is also called “account warming,” helping platforms recognize you as a normal user.
Step 5: Environment Detection (Strongly Recommended)
Before official operations, use ToDetect to check environment risks:
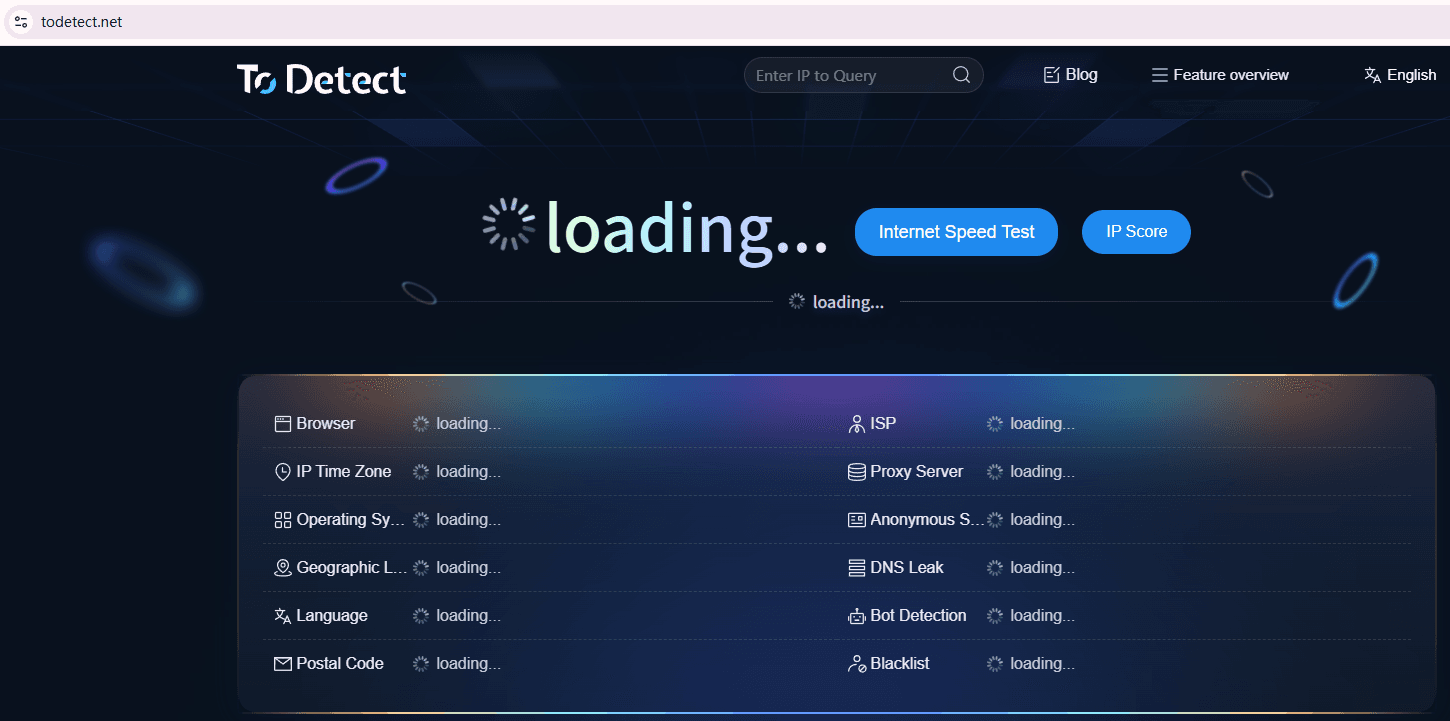
• Whether real device information is exposed
• Whether high-risk fingerprint duplication exists
If the results show Canvas anomalies, WebRTC leaks, or timezone/IP mismatches, the environment is unsafe and should be rebuilt.
Step 6: Start Matrix or Business Operations
Once the environment is stable, you can move into actual operations.
1. Social Media Matrix Operations
TikTok multi-account content posting, Instagram account farming, Facebook page matrices
2. Cross-Border E-Commerce Operations
Multi-store management, multiple ad account testing, market-specific campaigns
3. Advertising Testing
Multi-account creative testing, audience A/B testing, reducing ban risks
6. Can This Model Still Make Money? Focus on These Key Points
1. Account Survival Rate Determines Whether You Can Even Talk About Profit
In cross-border projects, accounts must survive before traffic and conversions can happen. Platforms now evaluate:
• Whether browser fingerprint environments are consistent
• Whether Canvas/WebGL behavior is abnormal
• Whether cookies are clean
• Whether login behavior appears human
If your environment setup is poor, accounts can still get restricted or flagged even with fingerprint browsers.
👉 The first priority is account survival. Only accounts that survive have a chance to generate profit.
2. Operational Rhythm Is More Important Than Tools
Many people overlook this: platforms don’t ban you instantly — they observe your behavioral patterns.
❌ Wrong approach: adding大量 friends immediately, launching ads on day one, mass-copying content. These actions easily trigger fingerprint detection and behavioral risk control.
✔ Correct rhythm (closer to real user behavior):
• Days 1–3: Browse, like, light interactions
• Days 4–7: Publish small amounts of content
• After Day 7: Gradually increase operation intensity
Always make the platform feel that you are a normal human user, not a machine.
3. Risk-Control Awareness Determines How Far You Can Go
Modern platform risk control isn’t a one-time ban. Platforms continuously monitor IP changes, browser fingerprint resets, and suspiciously synchronized behavior.
If you lack risk-control awareness — using a US IP today and suddenly switching to Europe tomorrow, constantly resetting fingerprints, or operating multiple accounts with identical rhythms — you can easily be flagged as “unnatural behavior.”
4. People Who Truly Make Money Usually Get These Three Things Right
Environment Standardization: Fingerprint browsers + stable IPs + fixed templates
Human-Like Operations: Behave like real users instead of automated machines
Traffic Scalability: Build reproducible account models instead of managing just 1–2 accounts
7. Fingerprint Browser FAQ (Questions Many People Ask)
1. Does Using a Fingerprint Browser Mean Accounts Will Never Get Banned?
No. Fingerprint browsers only reduce account-linking risks. They are not “anti-ban tools.” Platforms still evaluate IP quality, operational habits, account activity, and overall behavior.
2. Is It Difficult for Beginners to Learn Tools Like BitBrowser?
Not really. BitBrowser has a graphical interface: creating environments only takes a few clicks, IP binding has tutorials, and no coding knowledge is required.
The real challenge isn’t the tool itself, but understanding the logic of “one account = one independent environment.”
3. Is Browser Fingerprint Detection Really Necessary?
Yes, it is highly recommended. Many beginners skip this step and encounter account issues immediately after registration.
Detection tools like ToDetect can help identify whether real device information is exposed, whether fingerprints are duplicated, and whether the environment is easy to detect.
Conclusion
Fingerprint browsers are only the infrastructure of cross-border projects. What truly determines profitability is operational ability and risk-control awareness.
If you are a beginner, start with one account environment first. Learn how to build browser fingerprint environments and complete the detection process before gradually scaling up.
In the cross-border industry, the truly valuable thing has never been the tool itself — but how you use the tool within your business model.